Trezor Login: A Step-by-Step Guide to Securely Access Your Crypto Wallet
Introduction
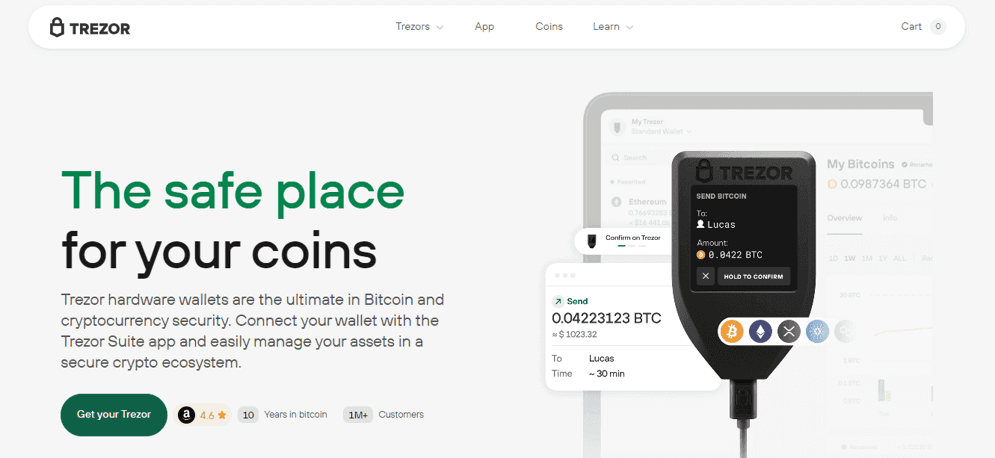
In the rapidly evolving world of cryptocurrency, securing your digital assets is critical. Trezor hardware wallets provide one of the most reliable solutions for safeguarding private keys offline. To manage your funds and access your wallet, you use the Trezor Login system, which works through the official Trezor Suite application. Unlike conventional logins, this system is device-based, providing a high level of security against cyber threats. This guide explains what Trezor Login is, how it works, and the steps you need to take to access your wallet safely.
What Is Trezor Login?
Trezor Login is a secure authentication method that allows users to access their wallet through Trezor Suite. Unlike online platforms that rely on usernames and passwords, Trezor Login requires:
A Trezor hardware wallet
Your PIN code
The Trezor Suite application
This combination ensures that private keys never leave the device. All sensitive operations, including sending crypto or verifying transactions, happen within the secure hardware environment.
Why Trezor Uses Hardware-Based Login
Hardware-based login significantly reduces the risk of theft or hacking. Since the private keys remain offline:
Hackers cannot access your funds remotely
Malware on your computer cannot intercept your login
Phishing attacks are less effective
Trezor Login also requires physical confirmation on the device for every critical operation. This ensures that even if someone gains access to your computer, they cannot perform transactions without your approval.
Step-by-Step Guide to Trezor Login
Step 1: Download and Install Trezor Suite
The first step is to install Trezor Suite from the official Trezor website. Trezor Suite is compatible with:
Windows
macOS
Linux
There is also a web version, but the desktop application is recommended for maximum security. Avoid downloading from unofficial sources, as counterfeit apps may compromise your funds.
Step 2: Connect Your Trezor Device
Use the USB cable provided with your hardware wallet to connect your Trezor device to your computer. The Trezor Suite application will automatically detect the device and prepare for authentication.
Step 3: Enter Your PIN
Your PIN code, created during initial setup, is required to unlock the device. This adds a layer of protection in case your wallet is lost or stolen. Enter the PIN directly on the device screen, not your computer.
Step 4: Confirm Access in Trezor Suite
Once the PIN is entered, Trezor Suite will ask you to approve the login. Confirm the request on your Trezor device. This step ensures that only someone physically holding the device can complete the login.
Step 5: Access Your Dashboard
After successful login, you will see your Trezor Suite dashboard. Here, you can:
View your portfolio and balances
Add or manage cryptocurrency accounts
Send and receive funds
Track transaction history
Adjust security settings
All critical actions still require confirmation on the hardware device, maintaining maximum security.
Key Features Available After Trezor Login
Portfolio Management
Trezor Suite provides a clear overview of your holdings. You can monitor each cryptocurrency’s value, track performance, and analyze your overall portfolio.
Secure Transactions
When sending crypto, Trezor requires you to verify and approve every transaction on the device itself. This protects against unauthorized transfers, even if your computer is compromised.
Multi-Currency Support
Trezor wallets support a wide variety of cryptocurrencies, including Bitcoin, Ethereum, Litecoin, and many ERC-20 tokens. After login, you can manage multiple accounts and track diverse assets in one place.
Staking and Rewards
Some cryptocurrencies allow staking directly through Trezor Suite. After logging in, you can delegate tokens and earn rewards while maintaining the security of your private keys offline.
Firmware Updates and App Management
Trezor Login also allows you to manage your device firmware and install or remove apps for specific cryptocurrencies. Keeping the firmware updated ensures your wallet remains secure and compatible with the latest tokens.
Troubleshooting Trezor Login Issues
Device Not Detected
Try a different USB port or cable
Restart Trezor Suite
Ensure the firmware is up to date
Incorrect PIN
Entering the wrong PIN multiple times triggers a device reset. You can restore your wallet using your recovery seed if this occurs.
Trezor Suite Won’t Open
Reinstall the application
Check your operating system for updates
Disable any conflicting antivirus software
Connection Problems
For web versions using WebUSB, make sure your browser supports it and no extensions block access. Using the desktop app avoids these issues.
Best Practices for Secure Trezor Login
Never share your recovery seed with anyone
Keep your PIN confidential
Verify all addresses on the Trezor device screen before sending funds
Store your hardware wallet in a secure location
Only download Trezor Suite from the official website
Following these practices ensures the highest level of protection for your assets.
Conclusion
Trezor Login provides a secure and reliable way to access your cryptocurrency holdings through Trezor Suite. By combining a hardware wallet, PIN authentication, and offline key storage, Trezor protects your digital assets from online threats and unauthorized access. From sending and receiving crypto to staking and tracking your portfolio, Trezor Login ensures that every action is secure and verified. Understanding this process is essential for anyone using a Trezor wallet, giving you confidence and control over your crypto investments.